Application & Experience
Visual workflows, business rules, decision tables, UI design, user journeys, and evolving data models.

Design processes, embed intelligence, and run business-critical applications on one unified platform. Built for complexity, change, and control.
Enterprise applications are shaped by years of business rules, integrations, regulatory constraints, and operational dependencies. Requirements change frequently, but traditional development and stitched tools make every change slow and risky. Most platforms automate tasks or add AI as a separate layer. Stackyon was built to treat workflows, decisions, and intelligence as core parts of the system so applications can evolve without losing structure, transparency, or control.
Meet the Stackyon Platform
The Stackyon platform is accessed and used through two tightly integrated components.
A visual, model-driven workspace where applications are designed and evolved—covering workflows, rules, data models, and user journeys.
Learn moreStep 1
Model how your business operates using processes, rules, and data.
Step 2
Embed intelligence where validation, judgment, or recommendations are required.
Step 3
Connect to existing applications, APIs, and data sources without disruption.
Step 4
Run applications reliably across environments.
Step 5
Adapt workflows, logic, and user experiences as requirements evolve without rewrites.
Stackyon provides the full set of capabilities required to build, modernize, and operate intelligent enterprise applications.
Visual workflows, business rules, decision tables, UI design, user journeys, and evolving data models.
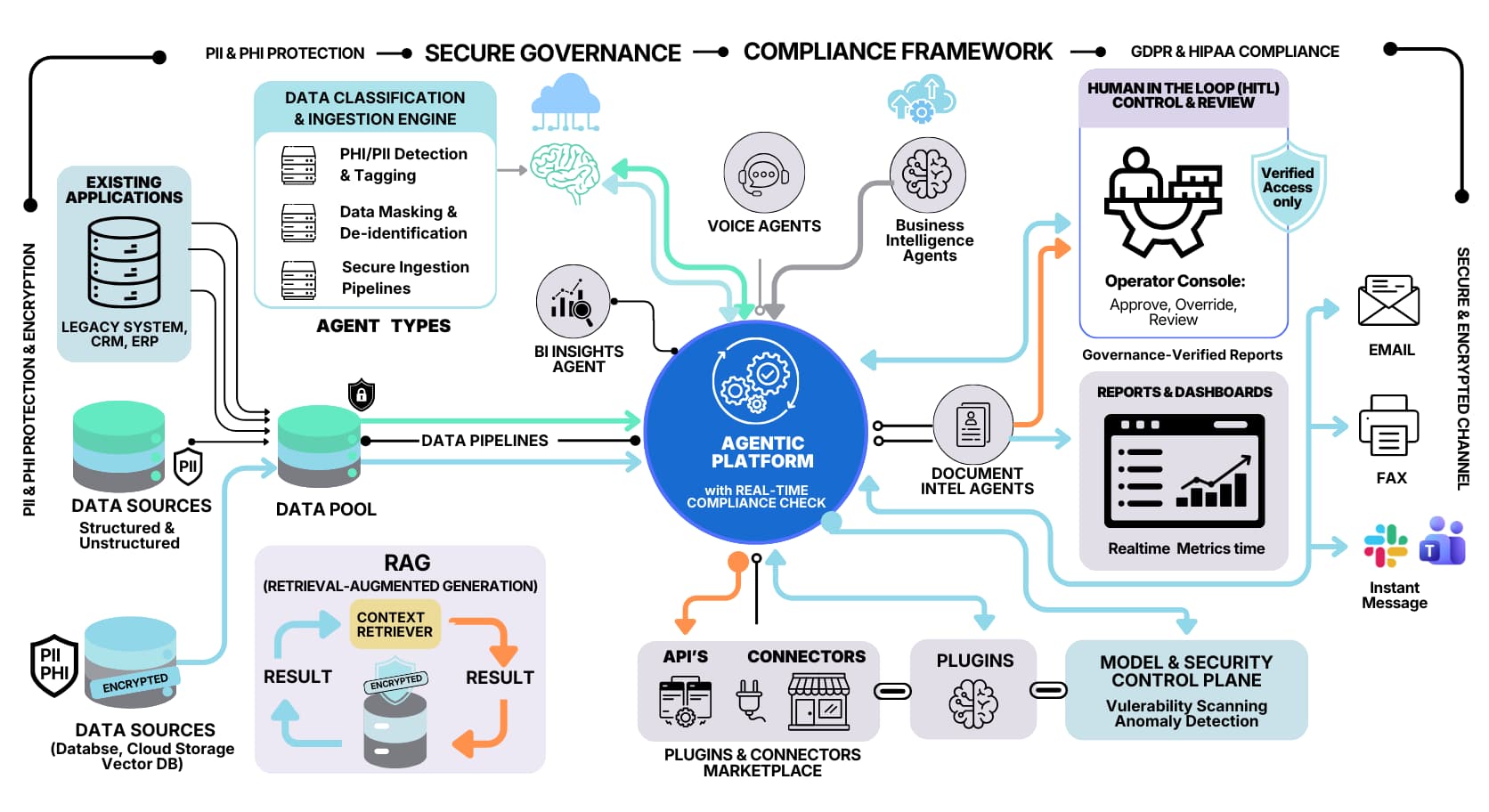
Agentic AI operating alongside rules and process logic for validation, recommendations, and decisions.
Support for conditional, parallel, and long-running execution reflecting real enterprise operations.
APIs and system integrations without disrupting existing enterprise environments.
Deployment, environment management, security, access control, auditability, and versioning.
Reporting, analytics, and observability across live applications.
Build smarter, modernize faster, automate intelligently.